Endpoints Are Too Easily Compromised
The Information Security team at any modern enterprise is acutely aware of the ever-present and increasingly sophisticated threats posed by hackers and rogue actors. As cyber warfare is widely recognised as a powerful political tool, the allocation of support by some governments towards state sponsored hacking activities is now immense. The challenge faced by organisations today in trying to protect their information, intellectual property and clients from cyber malfeasance is incredibly daunting. Hence the complex cyber security ecosystems that most enterprises currently leverage to - protect their endpoints from 5th generation cyber attacks.
Cyber attacks take many forms and target many different points of entry. However what has become recognised as a soft underbelly for cyber attackers is the endpoint. According to the IDC around 70% of successful breaches actually originate from the endpoint – a staggering figure when viewed in isolation. When taken in the context of the complex mix of tools that comprise a typical enterprise cyber security architecture, and combined with the persistent use of external and internal vulnerability assessments, that 70% figure is even more perplexing.
So how do these endpoints continue to be breached easily, despite the cyber security tools already deployed?
The Windows Group Policy architecture is widely used across enterprises to provide structure and consistency to the configuration of endpoints. Importantly, Group Policy is depended upon to control a host of different key security parameters on endpoints. Yet current toolsets do not audit endpoints for vulnerabilities derived from Group Policy. Instead, most organisations presume that their configuration is fully secure and that the configuration is being successfully applied to endpoints. That’s a risky strategy indeed and one truly appreciated by hackers.
Gytpol Validator is an innovative cyber security platform which has been specifically developed to identify commonly exploitable vulnerabilities across endpoints – in a way that no other tools in the market currently do. Its uniqueness is born very much from its creator’s background in both the military, and as she now calls herself, as a former hacker.
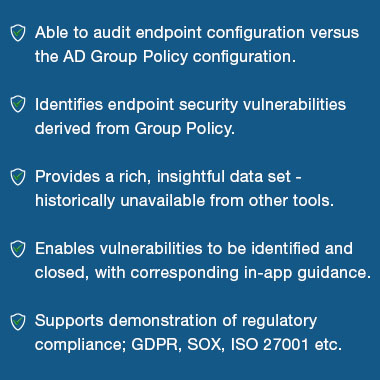

Amongst those organisations that have already deployed Gytpol Validator, approximately 90% of their endpoints are found to have vulnerabilities on the first scan of their estate – the majority of which were yet to be discovered. Gytpol is both a revelation and a wake up call for the companies that have deployed it. On initial scan, Information Security teams are quickly made aware of a broad spectrum of exploitable holes in their endpoint security which no other tools have identified. These are the same holes that hackers actively target because of a serious historic blind spot in vulnerability scanning tools.